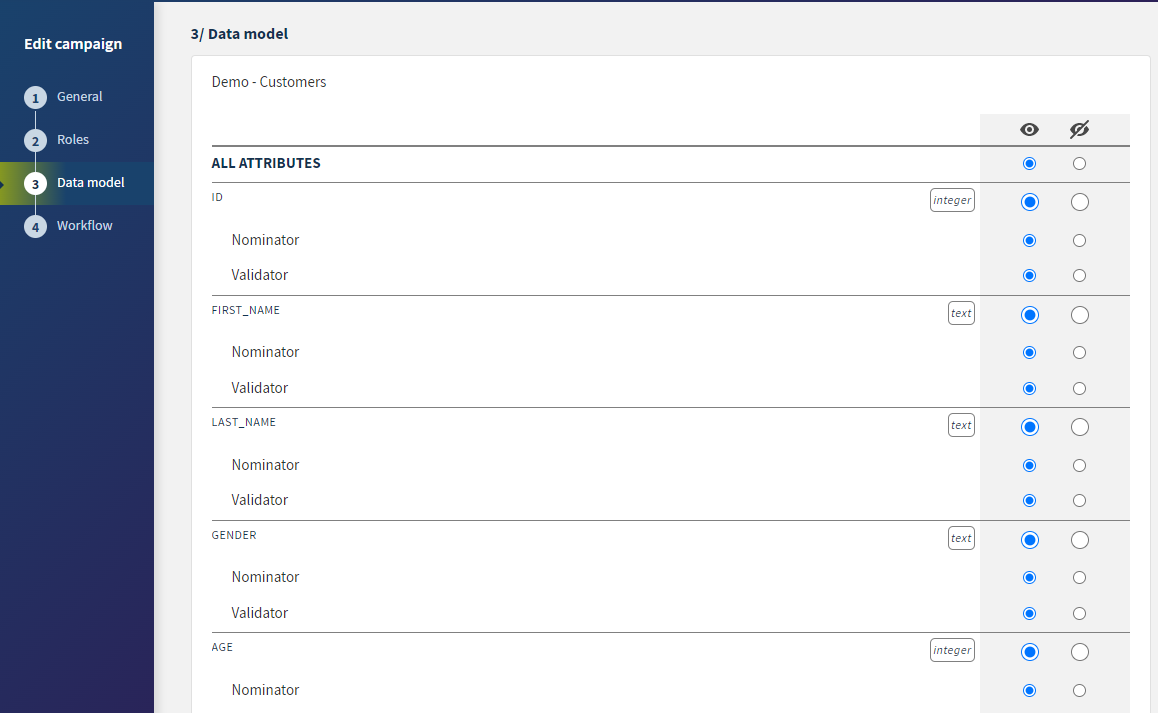
Setting a data model in the Arbitration campaign
Data models decide the structure of the data to be managed. They are used for the syntactic and semantic validation of data.
You can define the access permission per role to each of the attributes listed in a data model.
Procedure
Example
Did this page help you?
If you find any issues with this page or its content – a typo, a missing step, or a technical error – let us know how we can improve!