CA SiteMinder/Talend Administration Center SSO configuration Overview
This article explains how to configure CA SiteMinder to implement Single-Sign On with Talend Administration Center.
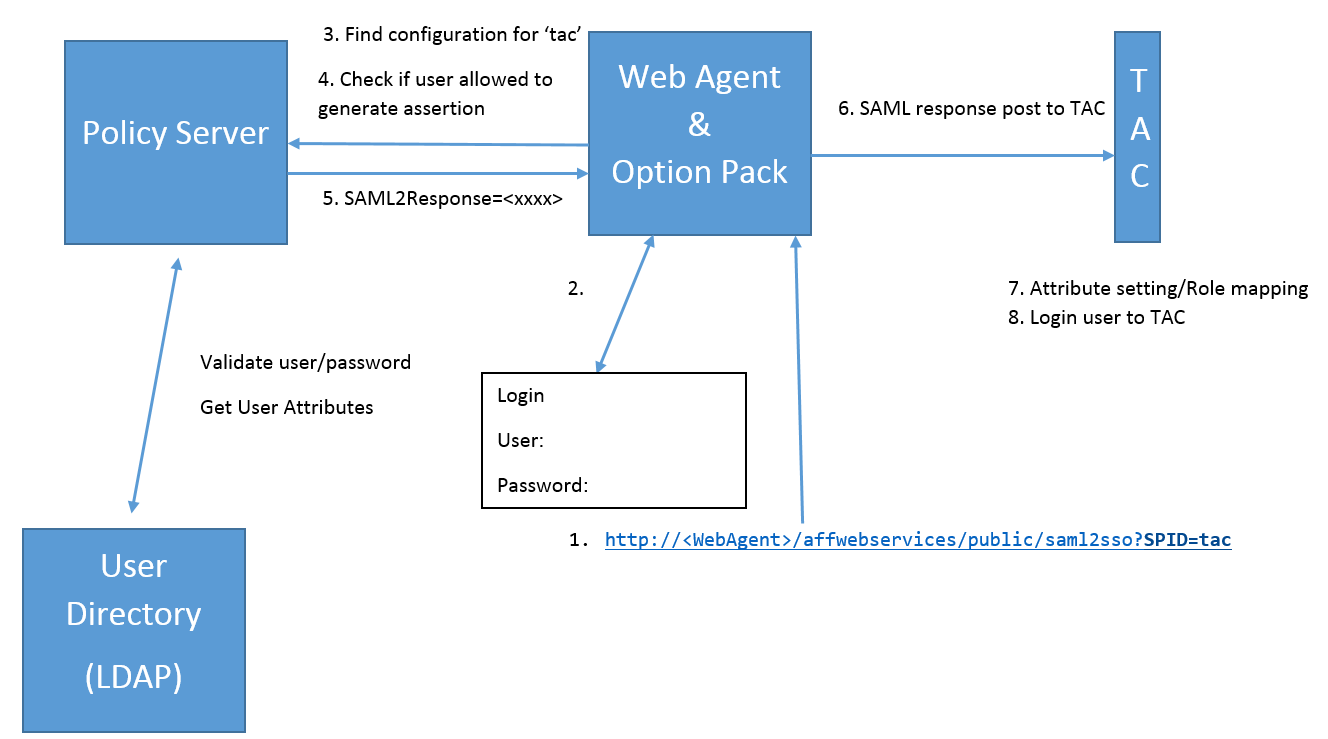
CA SiteMinder Partnership Federation is used to construct a SAML 2.0 identity provider (IdP), in order to generate assertions for users.
These assertions are sent back to Talend Administration Center, where user settings and roles are assigned based on the SiteMinder configuration.- The SSO process is initiated through a hard-coded link (e.g. http://host*/affwebservices/public/saml2sso?SPID=<SPEntityName>).
- This link redirects to the authentication page.
- If no user sessions exist, the user is redirected to the login page.
- When the user inputs valid credentials, there is a redirection to the assertion service (e.g. http://host1/affwebservices/public/saml2sso) and the assertions are generated.
- Assertions are formatted to an SAML 2.0 response in an auto-post form.
- Talend Administration Center gets SAML response when the form is submitted.
- Talend Administration Center retrieves attributes from the SAML 2.0 response, updates user attributes, processes role mapping.
- The user can then log in to Talend Administration Center.
1 is the host name or IP address of the server where Web Agent were
installed.
Did this page help you?
If you find any issues with this page or its content – a typo, a missing step, or a technical error – let us know how we can improve!
