Using SSO to log in to Talend Administration Center
Procedure
- On the Talend Administration Center, click Go to db config page.
-
Type in the administrator password (admin by default) in the Database
Configuration page and click OK.
If you want to change the default password that allows you to change the database configuration (recommended), you have to edit the database.config.password parameter value in the configuration.properties file. For more information, see Change the default password used to configure the database.After the first connection, the node.identifier property is added in the configuration.properties file, identifying the Talend Administration Center instance connected to the database. The node ID is also shown at the bottom of the tree view of Talend Administration Center.
-
Click the SSO node,
configure it, then click Save to save
your changes in the database:
Field
Value
IDP metadata
Click Launch Upload and upload the Identity Provider metadata file you have previously downloaded from the Identity Provider system.
Service Provider Entity ID Enter the Entity ID of your Service Provider (available in the configuration of the IdP).
For example, http://<host>:<port>/org.talend.administrator/ssologin in Okta and ADFS or <Connection ID> in PingFederate .
IDP Authentication Plugin
Select the Identity Provider from Okta, ADFS, ADFS3, ADFS4 PingFederate, Keycloak, SiteMinder, NetIQ and Custom plugin in the drop-down list.
If Custom plugin is selected, a Upload IDP Authentication Plugin dialog box will be shown prompting you to upload the custom Identity Provider metadata file. If Keycloak is selected, follow step 5 of this link to enable Personal Access Token.
The jar files provided by Talend are located in the <TomcatPath>/webapps/org.talend.administrator/idp/plugins directory.
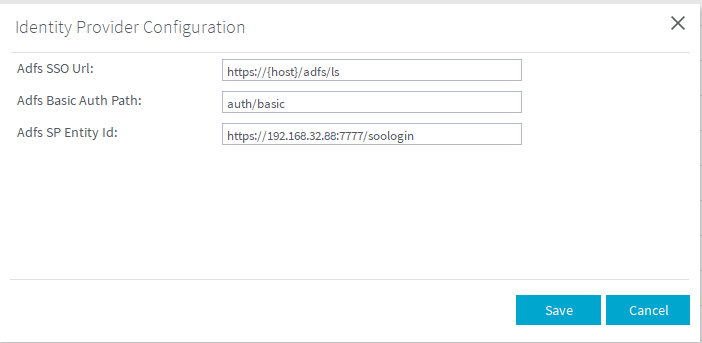
Identity Provider Configuration
Click Identity Provider Configuration and fill out the required information.
Example with PingFederate:- PingFederate SSO URL: https://win-350n8gtg2af:9031/idp/startSSO.ping?PartnerSpld=TAC701
- Basic Adapter Instance ID: BasicAdapter
Example with Okta:- Okta Organization URL: https://dev-515956.okta.com
- Okta Embedded URL: https://dev-515956.oktapreview.com/home/talenddev515956_talendadministrationcenter_1/0oacvlcac5j52hFhP0h7/alncvlmpk1VXbYAGu0h7
Example with AD FS 2:- Adfs SSO URL: https://<host>/adfs/ls
- Adfs Basic Auth Path: auth/basic
-
Adfs SP Entity Id:
https://<host>:<port>/org.talend.administrator/ssologin
Example with AD FS 3:- Adfs 3 SP Entity Id:https://<host>:<port>/org.talend.administrator/ssologin
- Adfs 3 SSO Url: https://<host>/adfs/ls
Example with AD FS 4:- Adfs 4 SP Entity Id: https://<host>:<port>/org.talend.administrator/ssologin
- Adfs 4 SSO Url: https://<host>/adfs/ls
Example with Keycloak:- Keycloak IDP initiated SSO URL: http://<host>:<port>/realms/myrealm/protocol/saml/clients/tac
- Assertion Consumer Service POST Binding URL: https://localhost:8080/org.talend.administrator/ssologin
Use Role Mapping
Set the value to true to map the application project types and the user roles with those defined in the Identity Provider system.
Mapping Configuration
Click Mapping Configuration and fill in the fields with the corresponding SAML attributes previously set in the Identity Provider system.
Once you have defined project types/roles at the Identity Provider side, you will not be able to edit them from Talend Administration Center.
Examples for project types:
- MDM=MDM; DI = DI; DQ=DQ; NPA=NPA
Examples for roles:-
Talend Administration Center Roles
- Administrator = tac_admin
- Operation Manager = tac_om
Setting the Talend Administration Center roles is mandatory.
-
Talend Data Preparation Roles
- Administrator = dp_admin
- Data Preparator = dp_dp
-
Talend Data Stewardship Roles
-
Data Steward = tds_ds
-
Role Mappings attributes: in case of a security identifiers list, you need to change the default value for SAML attribute name (tac.role) to tokenGroups.
The project types and roles set in the Identity Provider override the roles set in Talend Administration Center at user login.
Redirect URL on Logout In the Redirect URL on Logout field, enter the the URL of IDP you want to redirect browser to on logout from Talend Administration Center. If this field is empty, you will be redirected to the default location of Talend Administration Center on logout. If your organization does not accept custom attributes in the SAML token, either:- Select Show Advanced
Configuration in the wizard and, in Path to Value, enter the XPath
expression to target the SAML value to map to the corresponding Talend Administration Center object (Project
Types, Roles, Email, First Name, Last Name).
For instance, for DI project type: /saml2p:Response/saml2:Assertion/saml2:AttributeStatement/saml2:Attribute[@Name='tac.projectType']/saml2:AttributeValue/text()
- Set Use Role
Mapping to false.
In this case, you cannot create users manually, but the user type and the user roles can be edited in Talend Administration Center.
When users log in for the first time, their type is No Project access.
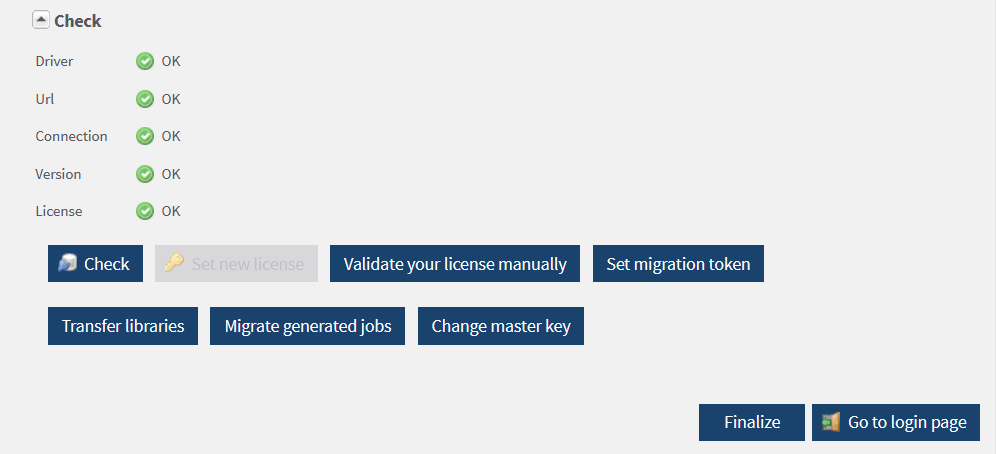
- If no license or an invalid license is found during the series of checks, you are prompted to specify a license. Click Set new license.
-
Click Browse to browse
to your license file and click Upload.
The license determines the types of users and projects you can manage in Talend Administration Center. For more information, see What domains can you work in depending on your user type and license.
-
Upon validation of your license, Talend Administration Center runs a series of checks
again, and displays the following options:
- Set new license: allows you to set a new license by repeating the previous step.
- Validate your license manually: allows you to validate the loaded license. For more information, see Generating a validation request.
- Transfer libraries: allows you to move external libraries stored on Nexus to the official Nexus repository where libraries are stored. For more information, see Migrating external libraries.
-
Make sure all the settings are correct, then click Finalize.
After finalizing the Database Configuration page, the option disappears form the login page. The Database Configuration page cannot be accessed anymore.If the license expires, you are redirected to the Database Configuration page by default, but only the license configuration option will be enabled.If some settings have to modified after finalization or to migrate external libraries, see Updating parameters after the configuration is finalized.
- Click Go to login page and type in the user credentials defined in your Identity Provider in the Login dialog box.
-
Click Login.
Talend Administration Center opens up on a welcome page.A pop-up window with a brief introduction to Talend Cloud is shown. If you are considering a move to Talend Cloud, click the link on the pop-up window for more information on the migration tools. Click Close to close the pop-up.
The menus and menu items shown vary according to the edition of Talend Administration Center currently in use. They also vary according to your role.
Did this page help you?
If you find any issues with this page or its content – a typo, a missing step, or a technical error – let us know how we can improve!
